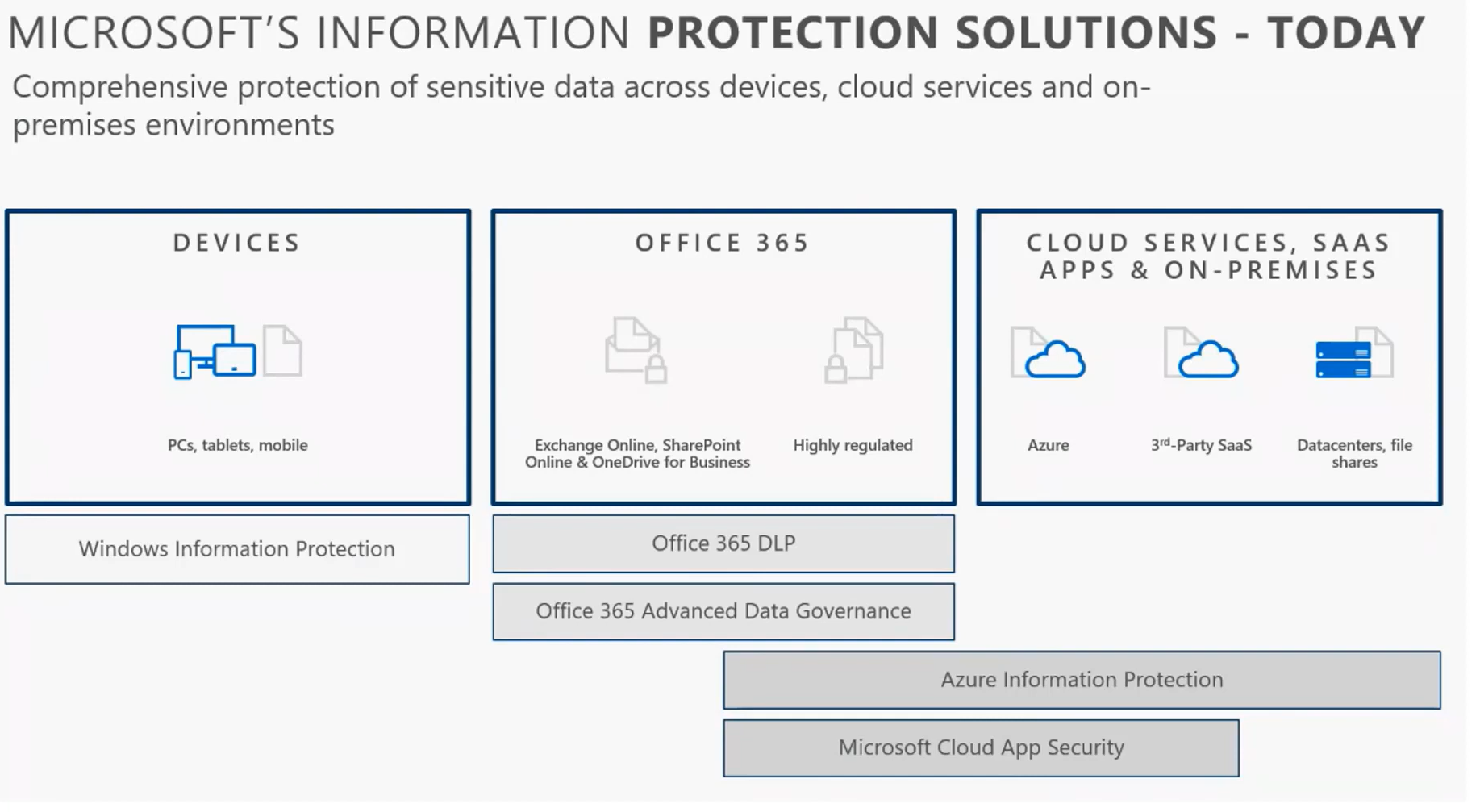
In previous blog posts, I have discussed the Azure Information Protection feature set with Microsoft Information protection. This feature set includes labeling and the AIP scanner you can run in an on-premise repository.
I have some suggestions for your first 30, 60, and 90 days when rolling out this portion of Microsoft Information Protection. I personally believe the largest struggle for MSPs and MIP is organization buy-in and adoption. End users can easily see applying labels to documents and having to navigate protections as a nuisance. Additionally, if the organization is not bought in the label taxonomy definitions or if they are not easy to understand, there will not be much success overall from on ROI standpoint.

First 30 Days
In the first 30 days I suggest working out the label taxonomy with organization leaders with the understanding that it could change based on feedback from the broader audience as you slowly roll it out to end users. You could very well adopt the default labels that Microsoft provides and in some cases, you may only tweak the names of these labels slightly. Some general guidelines to follow is to keep the label count to about 5 and make sure that they make sense to the organization. If users are instantly overwhelmed or confused with the taxonomy, they will either not adopt the service, or they will begin to apply incorrect labels to documents. The additional suggestions in the first 30 days is just around the discovery of data. Leverage the AIP scanner if you have files on-prem and also leverage Cloud App Discovery to discover files in 3rd party locations. This will give you a baseline inventory to work from and, with MIP sensitive information types, you could begin to discover any sensitive information that may exist in these locations such as SSN, PII, etc. The final step here is to pilot the labels to a subset group within the organization. Ideally these should be some champions that will provide you targeted feedback on their experience so you can refine the labels if needed.
First 60 Days
Within the first 60 days, its important to take that feedback and reorganize your taxonomy if applicable. With these changes you are now ready to perform a broad deployment of the taxonomy without enforcing any hard requirements. What I mean by this is that you are not forcing users to apply labels to documents but rather giving them training and encouraging them to apply these labels as a best practice. MIP gives you this flexibility on this where you could actually force a user to classify a document before they are able to save if you really wanted to. Remember, we want to strike a good balance here of protection without inhibiting user productivity. During this time you will also provide the org a central location for feedback so you can add anything additional here to your data set.
First 90 Days
Lastly, within the first 90 days you should begin to institute auto-labeling which will both auto classify documents as well as provide users a recommendation if sensitive information is detected in documents that they are curating in the future. Take the feedback you have received in the first 60 days to refine training for end users to enhance their experience and enhance your rates of adoption. If you follow certain regulations, you may need to slowly put more restrictive protections in place such as requiring users to classify documents before they save like I previously mentioned. Additionally, there are other controls you can leverage in labels such as requiring users to provide a justification reason if they change a label to something else.
Conclusion
Labeling with MIP can be a powerful solution but it is also very complicated to implement in organizations. Leverage the phased roll out plan I provided here to give guidance on how you tailor this solution to your client environments. Ideally, you could begin to refine your rollout plan and documentation after a few customer deployments so that it will not take much tweaking in the future from a broad deployment across all customers.