
The Hidden MSP Ticket Problem Costing You Hours Every Day
47 SecondsThat is how long the average knowledge worker stays focused on any screen before switching. And after a significant interruption, it takes up to

47 SecondsThat is how long the average knowledge worker stays focused on any screen before switching. And after a significant interruption, it takes up to

What is a Subnet? A subnet, sometimes known as a subnetwork, is an specific area of a larger network. To put it more precisely, subnets

Understanding Network Topology The arrangement of nodes and connections inside a network, including both its logical and physical components, is referred to as its topology.
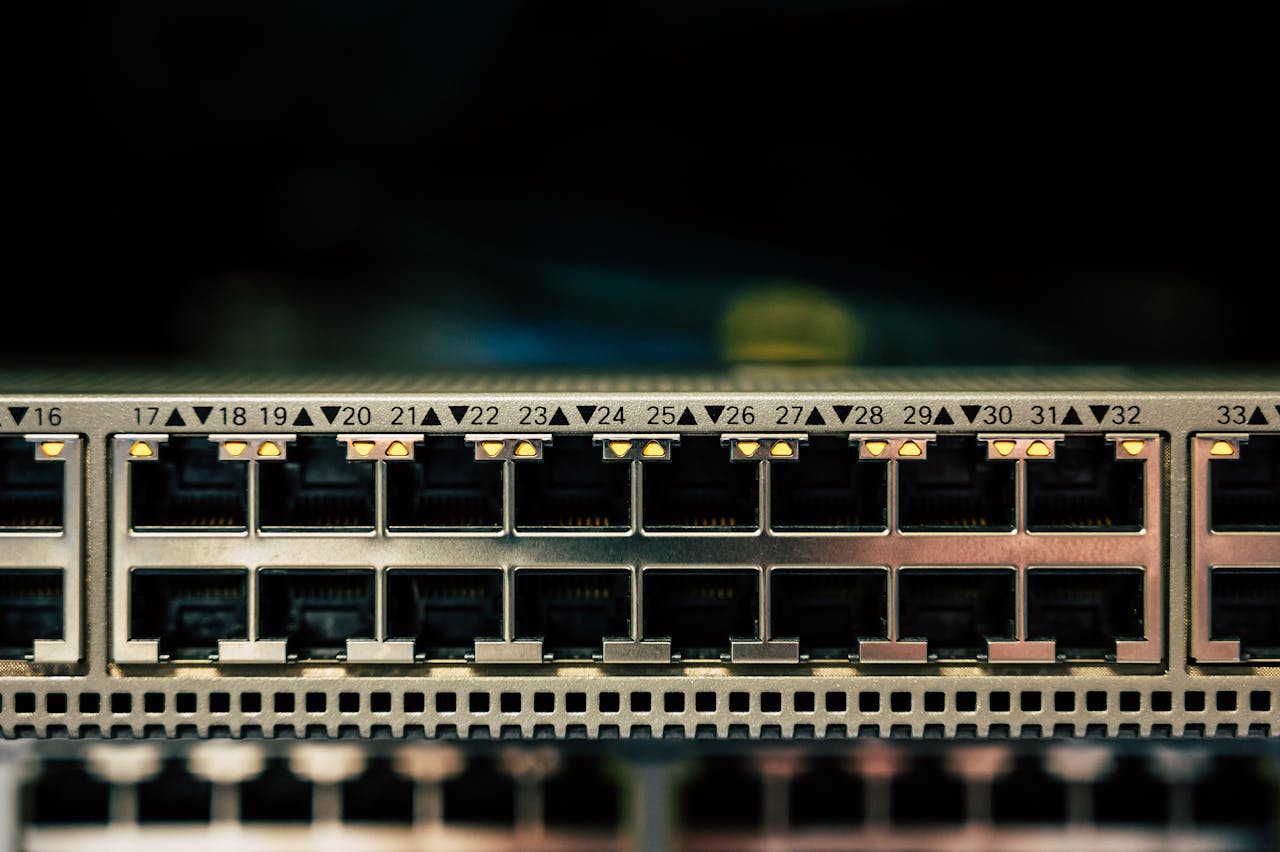
The term “trunking” is frequently used in the telecommunications and IT industries. Without depending on point-to-point connections, it explains a network configuration that effectively transfers

The two most important elements of additional security measures among the many network security advancements are encryption and hashing. With a digest size of 256
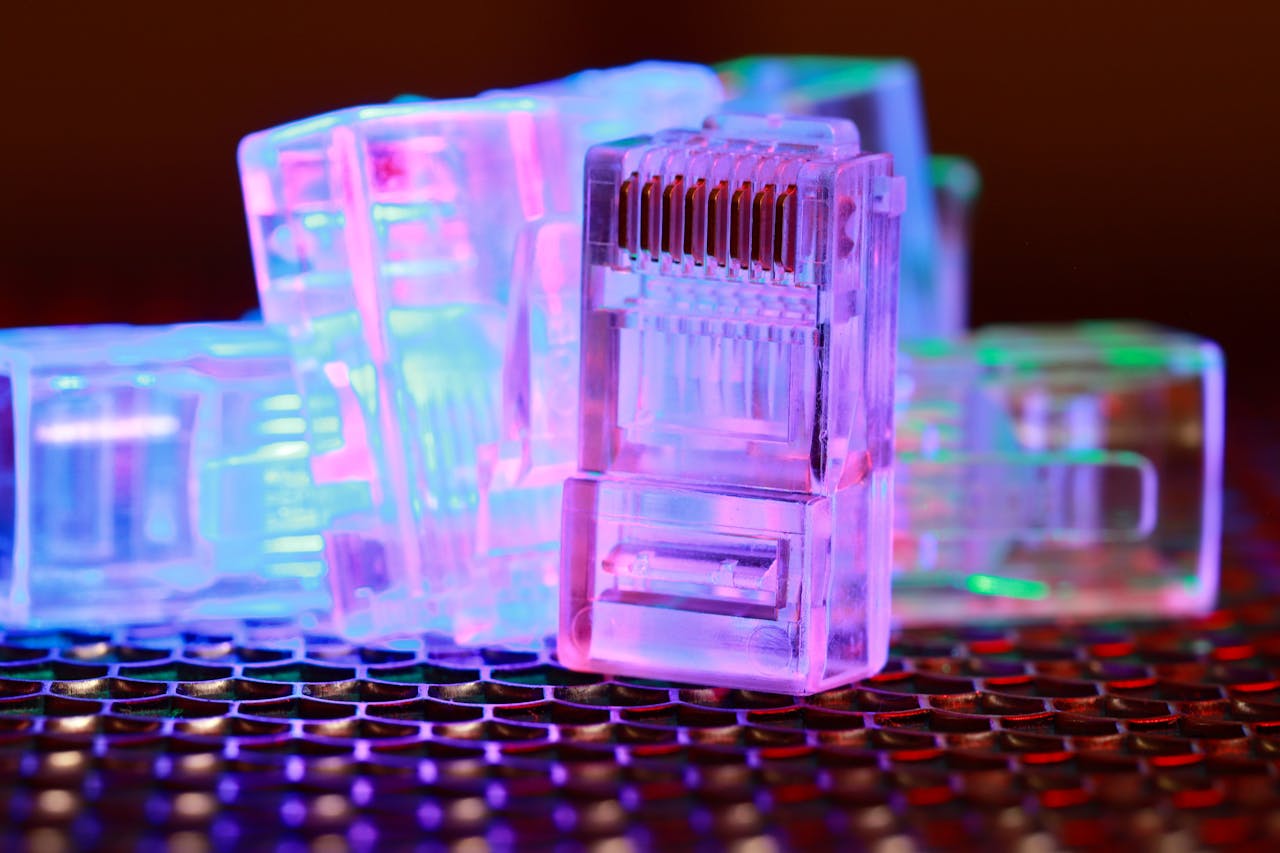
Definition VLAN (virtual LAN) A virtual LAN network overlay which groups a subset of devices that share physical LAN, separating traffic for each group. A

Very few companies have been able to gain people trust such as Google. As we can see in the past two decades google has only

There are majorly two backup strategies used incremental vs differential backup which are used for making frequent backups of data for disaster management. It systems

It’s possible that you have already experienced the frustration of losing important data if you are reading this. It’s possible that you accidentally erased it

Key Differences Between NTFS and FAT32 at a Glance NTFS and FAT32 are file systems, a file system is a way to arrange and specify

One of the most common and adaptable pieces of technology available today is the laptop computer. It can be used for a multitude of things